Attend IT Blog
Has your business dealt with a phishing attack? If not, consider yourself lucky. There has been a massive spike in phishing attacks as hackers are aggressively going after organizations and the personal identifiable information they hold. These attacks are just not focused on typical businesses either, they are going after organizations that provide public goods. One place that has become a major target for hackers (and phishing attacks) are schools.
At first glance, a college would be one of first places any hacker would look to steal information. Not only do today’s colleges have vast, powerful networks, they have many people that regularly compute on those networks who don’t take network security into account in the least. Despite the work of diligent IT administrators, the actions of the students and faculty on the network can really cause a lot of problems, so can direct attacks on the same students and faculty. For this reason, many colleges are starting to implement two-factor authentication procedures to ensure that even security-negligent college students aren’t putting their entire organization’s network at risk.
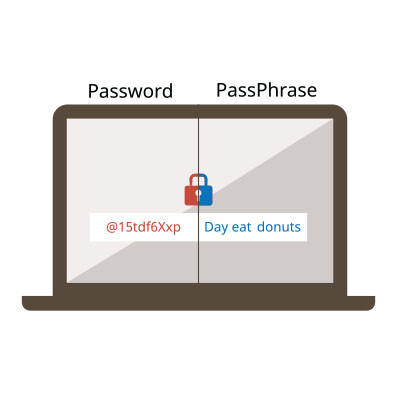
Two-factor authentication, for those who do not know, is the practice of requiring two steps to gain access to the network in the form of questions. The design is pretty simple, and has been around for a while. Traditionally, a user would type in a password which would prompt another access authenticator code. That electronic authenticator (also called, fob) would provide the user a code to use to access the door. Nowadays, most of the two-factor authentication credentials can be sent to an individual’s mobile device, as an overwhelming majority of people rely on smartphones.
In an article on KrebsOnSecurity, the Director of IT security and Infrastructure at Bowling Green University, Matt Haschak, stated that these attacks had grown from a relatively benign 250 in 2015 to over 1,000 in 2016. These attacks are carried out to steal credentials used to access BGSU’s MyBSGU portal, the main hub for student, staff, and administration affairs for the university. With these credentials, hackers can then infiltrate a system that is populated with thousands of people’s personal information.
Bowling Green isn’t the only example. Other universities have recently been targeted by what their IT security personnel calls “spear phishing” attacks, going after specific people associated with the college. This includes club officers, athletics administrators, and other people who would have access to “fast cash”. While IT administrators are cognizant of these relatively new threats, they tend to evolve and victimize before anything can be done about them.
One instance of this happened at the University of Delaware where scammers are targeting international students. These extortion attempts tell the target that if they don’t pay, they will face deportation under U.S. law. This shows that these attacks are specifically tailored to the recipients, making detection nearly impossible for IT administrators to ward against.
“This is something unusual,” UD IT communications group manager Richard Gordon said, “This is a scam that had not been seen at other universities before. It shows how these scammers are always looking for ways to try to hit students.” Gordon advocates diligence and integrating some type of two-factor authentication system for all accounts that hold sensitive information. “If the account information is stolen, then someone can get into your account. But if you have two-factor authentication, then they can’t access it because they need the extra security code. It’s an extra security piece.”
While college IT administrators have their hands full, your business is often considered low-hanging fruit for these hackers. If you want to learn more on how to protect your network, staff, and your business from these types of phishing attacks, contact our trusted team of IT technicians today. We can assess your current IT setup and consult with you on how to improve your organization’s network security. Call us today at 020 8626 4485.