Attend IT Blog
Network Drives: What All Those Letters Mean for Data Management
You often hear about “drives” when working with technology, but there are many different types that a computer might use in your business's day-to-day operations. Today, we want to explain what some of these drives do and why you should know where they are and what they stand for.
Why Know More About Drives at All?
Knowing what drives are on your computer will help you better navigate its data storage—especially if you’re connected to your business’ network infrastructure. Knowing what is internal storage and what is external or network storage will help you better locate important information if it’s stored internally.
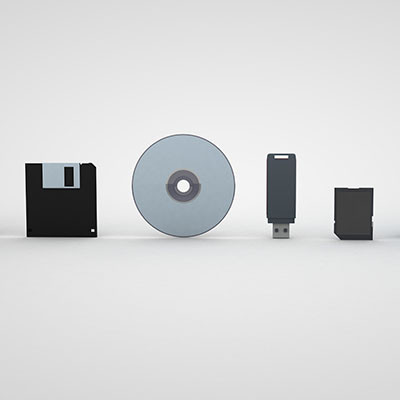
Depending on how old your device is, as well as its attached networking components, you will see different types of letters and drives. For example, most modern laptops have forgotten the disc drive (who carries CDs on them these days, anyway?). We’ll go over some of the ones you will see most commonly and some that are a bit obsolete. If you have these drives on your device, then perhaps we should be having a different conversation… one about how to upgrade you away from obsolete technology and into the modern computing era!
Fixed Drives vs Portable/Removable Drives
Your PC likely has a hard drive of some sort installed on it; this is what we would call a fixed drive, i.e. it’s built into the device itself and is unremovable. Portable or removable drives might include USB storage devices or SD cards.
To read data found on a drive, open up your File Explorer and navigate to This PC. You should see your available drives under Devices and Drives and any network-attached drives under Network Locations.
Keep in mind that this lettering system is arbitrary and doesn’t reflect all computers, but this is generally how it works:
The A: and B: Drives
Traditionally, the A: and B: drives were once used for floppy disc drives, and you won’t see them too often these days. At least, you shouldn’t be…
The C: Drive
It’s likely that the C: drive will be your primary hard drive. If your device has partitions set up on it, then there could be others after it, though, for each of your different partitions.
The D: and E: Drives
If your PC has a disc drive, then it will likely be assigned to either the D: or E: drive slot. Of course, if your device has a lot of different drives and partitions set up, then it could be something else, too, such as additional storage or partitions.
Other Letter Drives
After these initial drives, your operating system will start to assign drive letters based on chronological order. For example, if you plug in a USB thumb drive, and the next available letter is H:, then that will be your H: drive.
If you need help understanding your technology, Attend IT Limited is happy to help explain things further. To get started, reach out to us today at 020 8626 4485!
About the author